I found the issue. I had updated my eSet network security software and it enabled a firewall that prevented access to localhost. Once I turned off the firewall it worked fine.
Changing the port did not fix the issue.
I did that with the same result.
I also installed an update to MacOS (Sequoia 15.1) which restarted all processes on my machine. The problem still exists. I even tried to update abp suite but that didn't work either.
There are no client logs that I can find. Is there anything you can suggest to determine why the difference??
I sent you the output of the debug log. Do you have any idea why the login doesn't progress for the android?
iOS REQUEST/RESPONSE 2024-05-10 15:02:13.092 +00:00 [INF] Request starting HTTP/1.1 GET https://myproject.azurewebsites.net/connect/authorize?response_type=code&state=DGqPgPiUttg2Wy79OsLA2w&code_challenge=SX1FT89oOK6anVssPJ5dn7ZqenmPkjF5rgYrcTLRnjQ&code_challenge_method=S256&client_id=MyProject_Maui&scope=offline_access%20MyProject&redirect_uri=myproject%3A%2F%2F - null null 2024-05-10 15:02:13.093 +00:00 [INF] The request URI matched a server endpoint: "Authorization". 2024-05-10 15:02:13.093 +00:00 [INF] The authorization request was successfully extracted: { "response_type": "code", "state": "DGqPgPiUttg2Wy79OsLA2w", "code_challenge": "SX1FT89oOK6anVssPJ5dn7ZqenmPkjF5rgYrcTLRnjQ", "code_challenge_method": "S256", "client_id": "MyProject_Maui", "scope": "offline_access MyProject", "redirect_uri": "myproject://" }. 2024-05-10 15:02:13.127 +00:00 [INF] The authorization request was successfully validated. 2024-05-10 15:02:13.136 +00:00 [INF] Executing endpoint 'Volo.Abp.OpenIddict.Controllers.AuthorizeController.HandleAsync (Volo.Abp.OpenIddict.AspNetCore)' 2024-05-10 15:02:13.137 +00:00 [INF] Route matched with {action = "Handle", controller = "Authorize", area = "", page = ""}. Executing controller action with signature System.Threading.Tasks.Task`1[Microsoft.AspNetCore.Mvc.IActionResult] HandleAsync() on controller Volo.Abp.OpenIddict.Controllers.AuthorizeController (Volo.Abp.OpenIddict.AspNetCore). 2024-05-10 15:02:13.137 +00:00 [INF] Skipping the execution of current filter as its not the most effective filter implementing the policy Microsoft.AspNetCore.Mvc.ViewFeatures.IAntiforgeryPolicy 2024-05-10 15:02:13.138 +00:00 [INF] Executing action method Volo.Abp.OpenIddict.Controllers.AuthorizeController.HandleAsync (Volo.Abp.OpenIddict.AspNetCore) - Validation state: "Valid" 2024-05-10 15:02:13.145 +00:00 [INF] Executed action method Volo.Abp.OpenIddict.Controllers.AuthorizeController.HandleAsync (Volo.Abp.OpenIddict.AspNetCore), returned result Microsoft.AspNetCore.Mvc.ChallengeResult in 7.3277ms. 2024-05-10 15:02:13.145 +00:00 [INF] Executing ChallengeResult with authentication schemes (["Identity.Application"]). 2024-05-10 15:02:13.145 +00:00 [INF] AuthenticationScheme: Identity.Application was challenged. 2024-05-10 15:02:13.145 +00:00 [INF] Executed action Volo.Abp.OpenIddict.Controllers.AuthorizeController.HandleAsync (Volo.Abp.OpenIddict.AspNetCore) in 8.7755ms 2024-05-10 15:02:13.145 +00:00 [INF] Executed endpoint 'Volo.Abp.OpenIddict.Controllers.AuthorizeController.HandleAsync (Volo.Abp.OpenIddict.AspNetCore)' 2024-05-10 15:02:13.146 +00:00 [INF] Request finished HTTP/1.1 GET https://myproject.azurewebsites.net/connect/authorize?response_type=code&state=DGqPgPiUttg2Wy79OsLA2w&code_challenge=SX1FT89oOK6anVssPJ5dn7ZqenmPkjF5rgYrcTLRnjQ&code_challenge_method=S256&client_id=MyProject_Maui&scope=offline_access%20MyProject&redirect_uri=myproject%3A%2F%2F - 302 null null 53.7288ms 2024-05-10 15:02:13.214 +00:00 [INF] Request starting HTTP/1.1 GET https://myproject.azurewebsites.net/Account/Login?ReturnUrl=%2Fconnect%2Fauthorize%3Fresponse_type%3Dcode%26state%3DDGqPgPiUttg2Wy79OsLA2w%26code_challenge%3DSX1FT89oOK6anVssPJ5dn7ZqenmPkjF5rgYrcTLRnjQ%26code_challenge_method%3DS256%26client_id%3DMyProject_Maui%26scope%3Doffline_access%2520MyProject%26redirect_uri%3Dmyproject%253A%252F%252F - null null 2024-05-10 15:02:13.221 +00:00 [INF] Executing endpoint '/Account/Login' 2024-05-10 15:02:13.221 +00:00 [INF] Route matched with {page = "/Account/Login", area = "", action = "", controller = ""}. Executing page /Account/Login 2024-05-10 15:02:13.221 +00:00 [INF] Skipping the execution of current filter as its not the most effective filter implementing the policy Microsoft.AspNetCore.Mvc.ViewFeatures.IAntiforgeryPolicy 2024-05-10 15:02:13.260 +00:00 [INF] Executing handler method Volo.Abp.Account.Public.Web.Pages.Account.LoginModel.OnGetAsync - ModelState is "Valid" 2024-05-10 15:02:13.261 +00:00 [INF] Executed handler method OnGetAsync, returned result Microsoft.AspNetCore.Mvc.RazorPages.PageResult. 2024-05-10 15:02:13.281 +00:00 [INF] Executed page /Account/Login in 60.2635ms 2024-05-10 15:02:13.281 +00:00 [INF] Executed endpoint '/Account/Login' Health status requests begin after this
Microsoft changed the signature of the issuer from what it originally was and that caused the cert error.
Again, I have 2 apps that are built on the 8.0.x framework and neither of these app will run using the Android version locally. Both generate the same Java.Cert.CertificationException. I have used the abp.io commercial framework for 3 years but with the latest releases I have had more problems getting a working version of my MAUI apps. I have gotten the iOS versions of the apps to compile and run successfully without any certification exceptions, but the Android versions are failing.
I get the Cert exception and then get an Autofac exception:
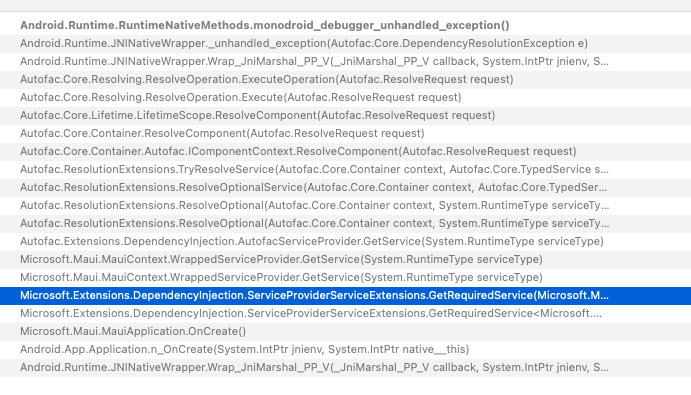
These occur immediately after the splash screen is displayed.
I continue to have the issue with the Cert error. This has not been an issue with previous versions of abp.io.

