and you can try to publish your angular&authserver website to internet. So I can check it online.
I have shared HRA and DEV URL over email please check.
hi
I'm off work(UTC+8) : (
Ok np we will connect tomorrow.
Can you try recording the har again?
I'm trying to record my screen, but once I open the network tab, it doesn't appear in the recording. Let me try one more time sharing it with you shortly.
Why do you have two har files?
After redirected anchor-admin-dashboard above request remove from network that's why share two hra file.
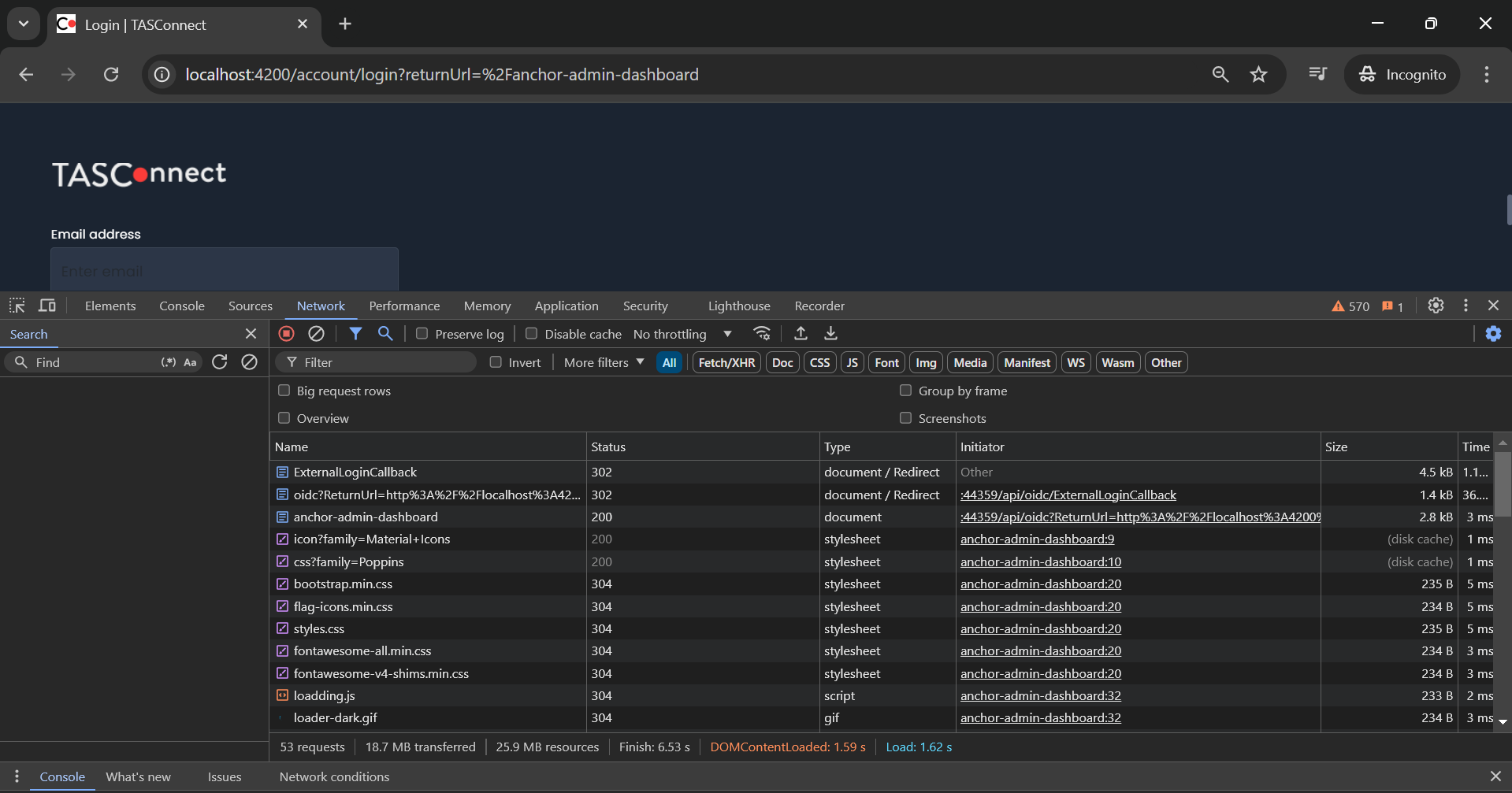
localhost:4200 -> login -> redirect - https://localhost:44333/Account/Login -> OpenIdConnect -> auth0.com(redirect url is https://localhost:44333/api/oidc/ExternalLoginCallback) signing at auth0 -> https://localhost:44333/api/oidc/ExternalLoginCallback -> http://localhost:4200/?code=UAbYI -> success
Hi, I have shared har over email please check and let me know if you required any other information.
Thanks.
hi
Can you share the
harfile again?The
redirect uriof the POC project and your previous request are different.Please re-record the har of your project.
Thanks.
As per our earlier discussion, you suggested that I change the approach. As a result, I moved all the code from the API to the Angular side, which is why the redirect URL is now different: http://localhost:4200/oidcredirect
However, we will set aside this approach for now. As per the POC project, we will follow the original approach.
Below is the POC redirect URL. We will now follow this POC code approach.
Same POC code i have implemented in my existing project. However, after redirect to dashboard, In My project connect/authorize and http://localhost:4200/?code=UAbYIzkcPox30xx API as well not call automatically from angular.
IF you see POC project in network tab you able to find out after redirect dashboard .
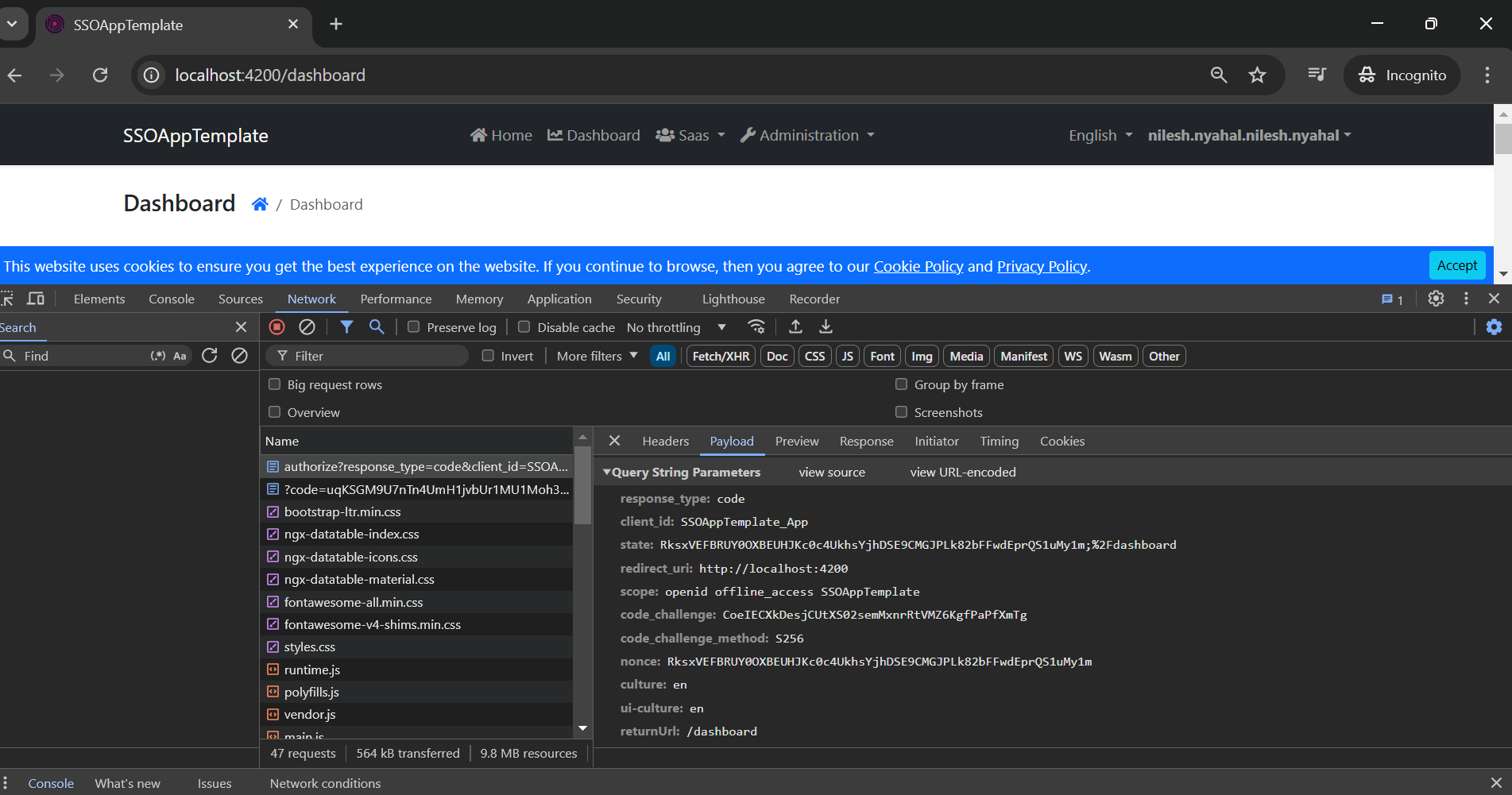 connect/authorize and and http://localhost:4200/?code=UAbYIzkcPox30xx automatically call from angular .
connect/authorize and and http://localhost:4200/?code=UAbYIzkcPox30xx automatically call from angular .
If i am correct how to resolved this or my observation is not correct ? pls suggest.
you successfully redirected to dashboard right ?

